rSAP XSUAA (SAP Cloud Platform XSUAA service) is a cloud-based service that enables secure authentication and authorization of applications and services running on the SAP Business Technology Platform (BTP). XSUAA offers comprehensive features and capabilities that allow developers to implement secure and robust authorization models for their applications and services.
In this blog, we will discuss the key components of XSUAA auth and how to implement SAP XSUAA authorization on BTP, a configuration of the XSUAA service in a CAPM (Cloud Application Programming Model) application, creation of a role-based access control (RBAC) model, and integration of the XSUAA service with the CAPM application deployed on BTP.
Key Components of XSUAA Authorization:
To implement XSUAA authorization on SAP BTP, we need to understand its core components:
a. Service Instances:
XSUAA service instances are the central management point for configuring authentication and authorization policies.
b. Roles and Scopes:
Roles and scopes define access privileges and permissions. Additionally, roles represent a set of permissions, while scopes represent fine-grained permissions for specific resources or actions.
c. Identity Providers:
XSUAA supports various identity providers, including SAP ID Service, SAML-based providers, and OpenID Connect providers. These providers enable user authentication and retrieval of user attributes.
d. JWT Tokens:
JSON Web Tokens (JWT) represent authenticated user information and authorization details. Applications can validate these tokens and extract relevant information to make access control decisions.
I recently came across a great example on the SAP Developers website that provides a walkthrough of the steps required to set up the XSUAA service.
-
Run the following command in the CAPM project folder:

Running cds add xsuaa command does two things
- Adds the XSUAA service to the package.json file
- Creates the XSUAA security configuration
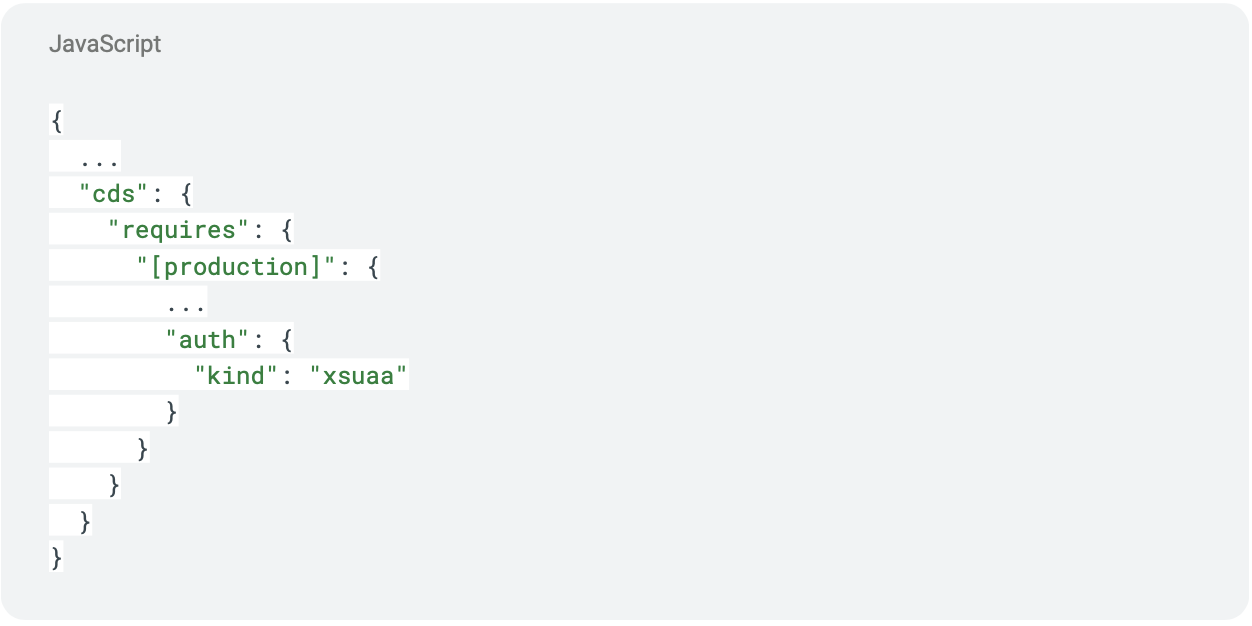
2. Check if the following lines have been added to the package.json in the project:
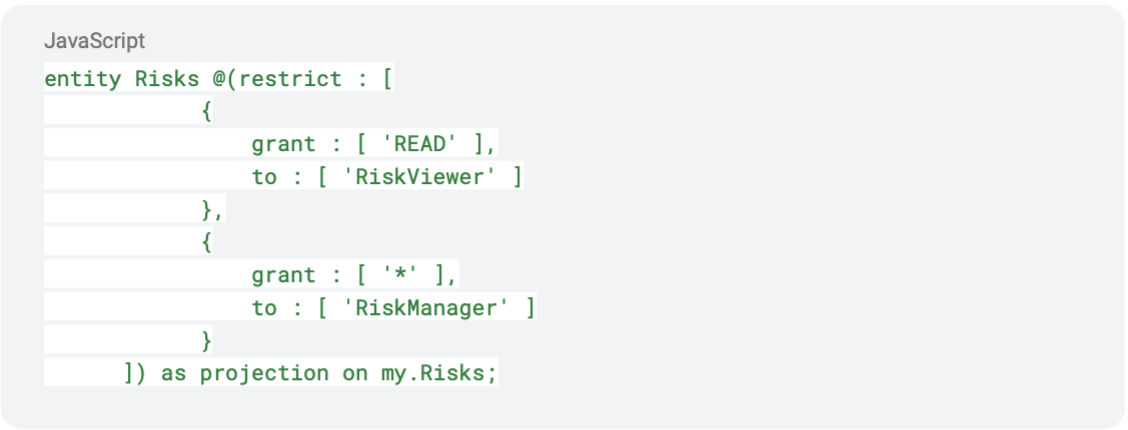
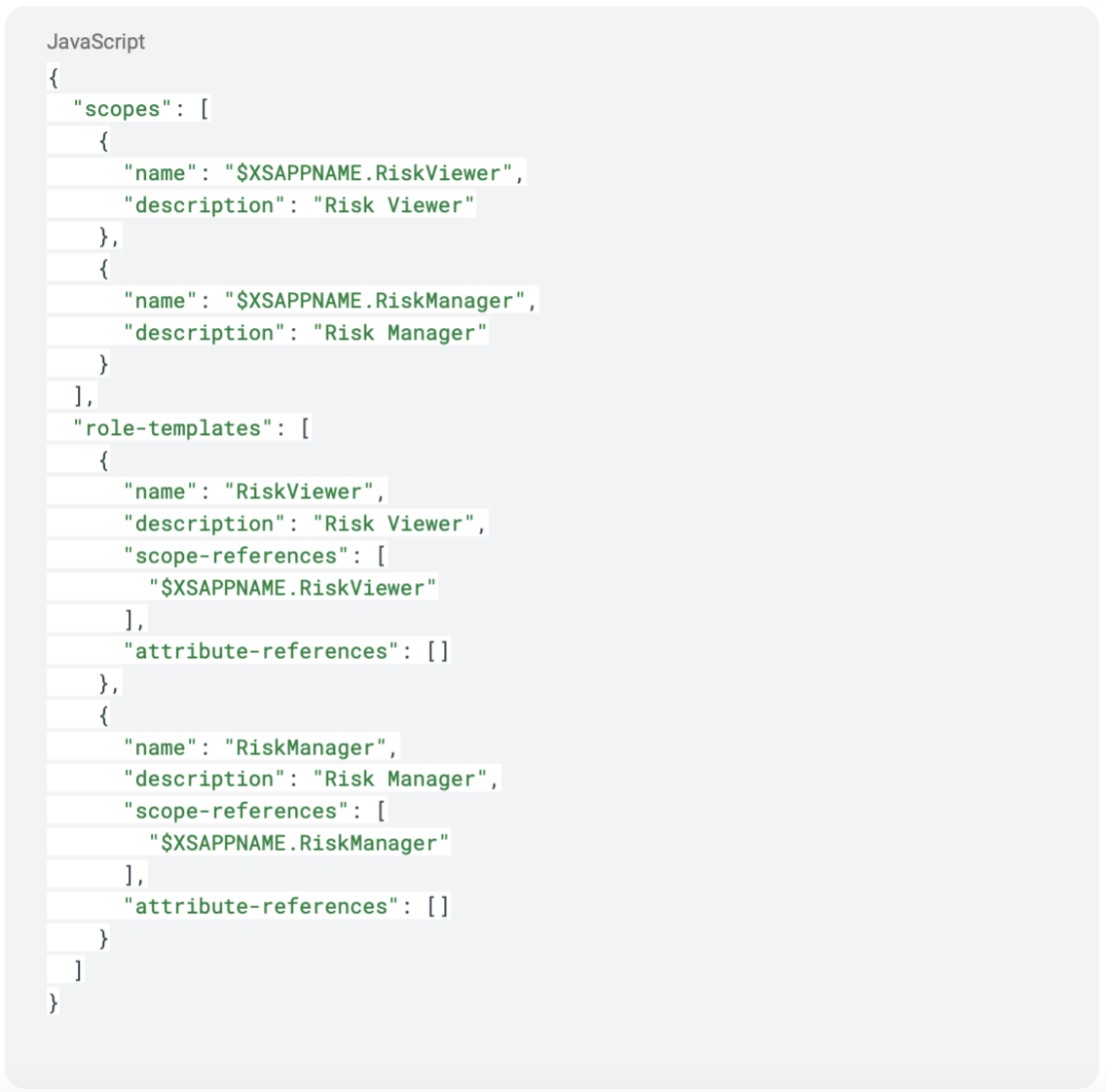
3. Check the file xs-security.json that was created in the CAPM project. The file contains the configuration of the XSUAA (XS User Authentication and Authorization Service). The CAP server takes the authorization parts @(restrict … ) from our service definition form and creates scopes and role templates. For example, it found the roles RiskViewer and RiskManager in the srv/risk-service.cds file:
4. And created scopes and roles for both in the xs-security.json file:
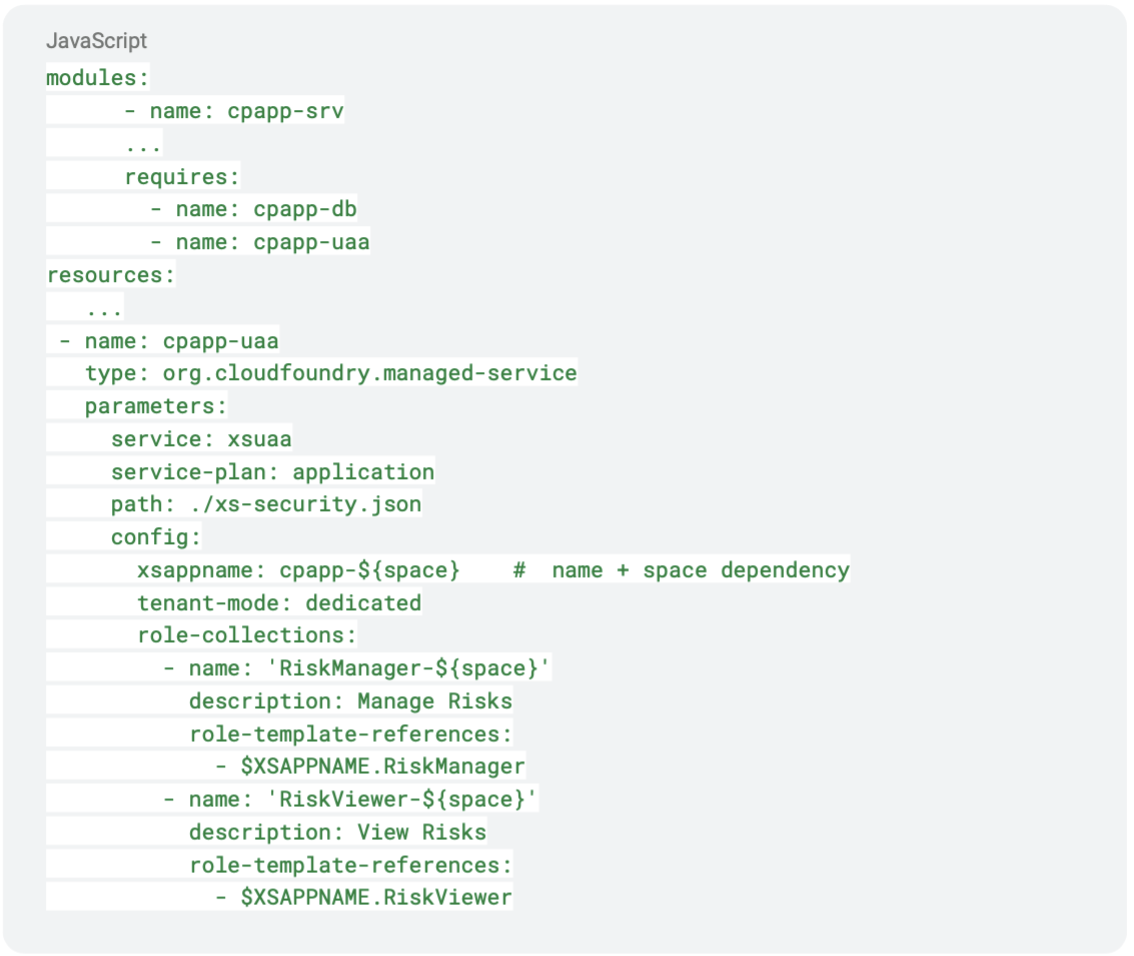
5. The next step is to add the Authorization and Trust Management service to mta.yaml to allow user login, authorization, and authentication checks. Update the name (from cpapp-auth to cpapp-uaa) and resource as shown.
6. Build and Deploy the MTA module. After successful deployment, check if the services are created correctly on BTP.
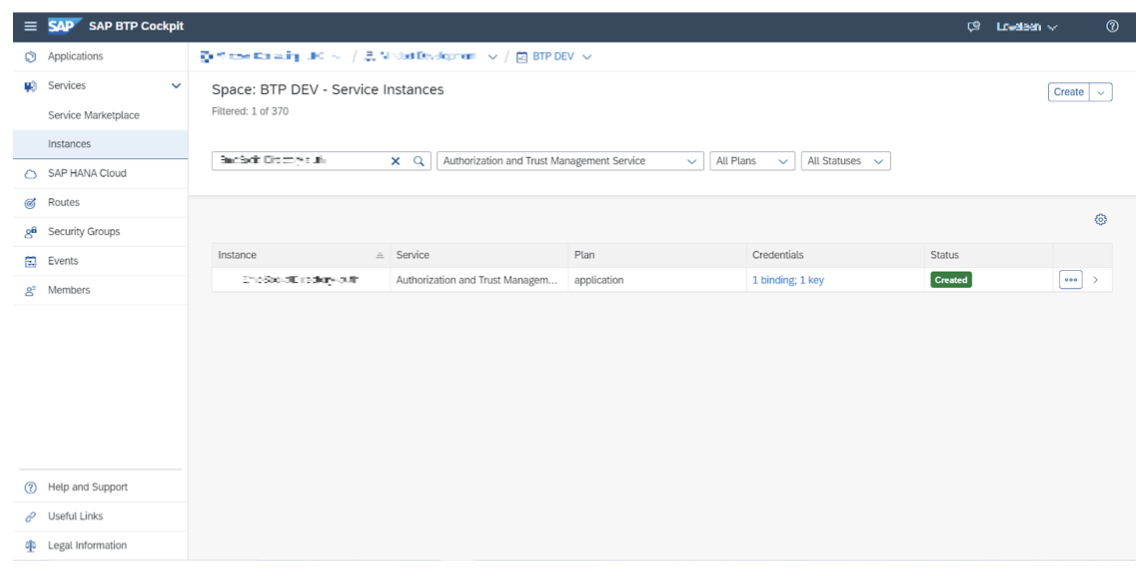
7. Roles are automatically generated in the SAP BTP cockpit using the xs-security.json file. However, the creation of role collections and assigning roles, users, or user groups is done manually within the Security section of the BTP sub-account.
8. To configure the destination for the deployed CAPM (Cloud Application Programming Model) service, choose the Authentication type as OAuth2JWTBearer. To obtain the required details like Client ID and Client Secret, you can retrieve them from the service instance.

SAP XSUAA is a powerful service that enables developers to implement secure and robust authorization.
Implementing XSUAA authorization on BTP requires a solid understanding of authentication and authorization concepts and the configuration and integration steps outlined in this blog. Following these guidelines, developers can build secure and scalable applications on the SAP Business Technology Platform.
View our LinkedIn, here.